CyberSecurity.pk a Information and cyber security consulting services – Governance, Risk, and Compliance Security Consulting Firm, Managed Security Services designed to create and adapt security strategy, addressing organization threats, risks, business objectives and risks to the security strategy.
from Cyber Criminals.
interference and re-productivity of the evidence.
web, network & infrastructure before you dark..
VirtualChief Information Security Officer
CyberSecurity.pk Operations Consulting Virtual Chief Information Security Officer CISO, with our VCISO service you retain a board-level resource who can ‘virtually sit inside your company’ and manage your security strategy, budget, review of risks and regulatory programs.
CybserSecurity.pk team has extensive experience with security leaders from a variety of industries, and we apply their knowledge to provide you a Virtual CISO. Working directly with your team, no matter the size, Our Virtual Chief Information Security Officer (vCISO) will help strategically plan, and execute the cyber security strategy that aligns with your business strategy. With our guidance, your organization will realize the best strategy to securly enable and support the business, while still dramatically reducing information security risk and inefficiency.
Our Virtual CISO / vCISO (Chief Information Security Officer) Consulting Services provide you:
We provide you with wide ranging expertise needed for incident response, compliance and the latest threat intelligence to address information security flaws and execute actionable mitigation strategies.
Data Governance, helping you handle increasingly large volumes of data and the related regulations, controls and disposition plans.
We Are Here For You
CyberSecurity.pk principles are designed to safeguard company data, websites and web applications from attackers seeking to disrupt, delay, alter or redirect the flow of data. These attackers vary in target, motive, levels of organization, and technical capabilities, requiring public and private organizations to adopt ever-increasing measures to prevent cyber attacks.
Our security governance team maintain cyber security measures to protect the integrity of critical infrastructure for financial systems, public health, science, and safety institutions, and defense, aerospace, and intelligence agencies
Our Consulting services provides you Information Security Strategy & Design to give you a better security posture.
Information Security Assessments to analyse the maturity of your information security program, as well as identify gaps, weaknesses, and opportunities for improvement.
Virtual CISO, which provides you with wide ranging expertise needed for incident response, compliance and the latest threat intelligence to address information security flaws and execute actionable mitigation strategies
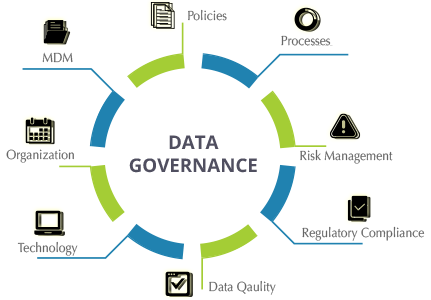
Data Governance, helping you handle increasingly large volumes of data and the related regulations, controls and disposition plans
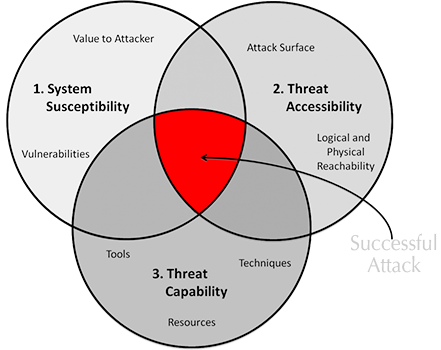
Threats, Vulnerabilities, and Risks
In the overwhelming sea of information, access to timely, insightful and independent open-source intelligence (OSINT) analyses is crucial for maintaining the necessary situational awareness to stay on the top of emerging security threats. Our security solutions are designed to catch and stop bad actors at the earliest possible point of attack.
Vulnerabilities
Software Bugs, Broken Processes, Ineffective Controls, Business Changes, Legacy Systems, Human Error
Threats
Hackers, Nature, Competitors ,Angry Employees, dishonest Employees, Criminals, Terrorists , the Press ,
Risks
Business Disruption, Financial Losses, Loss of Privacy, Reputation, confidence, legal penalties, Impaired Growth
Cyber Security Consulting Protect Your Assets, we know that cybercriminals can’t wait to get there hands on your data, we secure your data, and monitor the dark web just in case it does gets out.
Motivation BehindAttacks
Crypting ServicesExploit KitsCrimewareLeaked DataWeak passwordsSocial EngineeringMissing authorizationUnpatched SystemsConfiguration weaknessDownload of codes without integrity checksURL redirection to untrusted sites
— Cyber Security Vulnerabilities —
Are A Critical Component Team
During a breach, it’s important to move quickly to contain the threat and minimize the impact by getting to the root cause. However, overlooking evident procedures can limit your ability to help legal or governmental authorities pursue the threat actor.
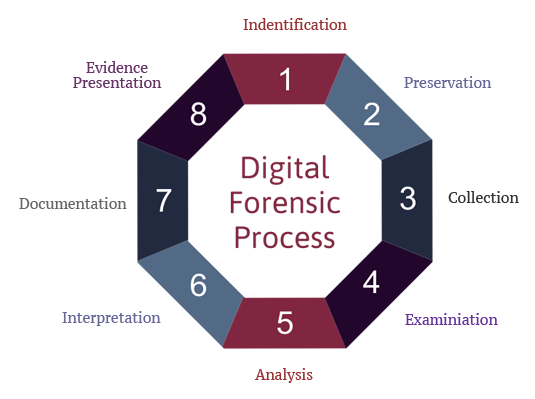
Our Digital Forensics Investigator’s first step is to clearly determine the purpose and objective of the investigation in a free consultation. We will work with you to identify where your data is located. We will document the legal chain of custody of the media and we will make a bit by bit copy and preserve the original. The Digital forensic analysis will examine and extract the data that can be viewed by the operating system, as well as data that is invisible to the operating system including deleted data that has not been overwritten.
Our Digital Forensics Investigator also addresses the legal issues associated with electronic evidence, such as relevant case law, how to navigate the discovery process, protection of privilege, and in general, working with attorneys and other professionals.
Our investigation team will thoroughly investigate the incident while keeping you informed of all results. Computer forensic investigation can be performed during Incident Response Handling or independently, depending on your needs. Our experts leverage elite cyber threat intelligence to investigate the breach, determine its likely cause , incorporate in standard report and help you contain and eradicate the threat from your environment as quickly as possible.
Keep Your Systems and Networks Current
There are many technical challenges facing organizations today. The requirement to transform critical infrastructure into networks capable of supporting next-generation applications and devices is contributing to an increasing complexity in network configuration management. There is pressure to reduce cost, coupled with limited funding to keep your systems and networks current. Our managed services can protect your investment and keep you running while you focus on your business.
Our customized managed service solutions include Virtualization, Networking, Security and Compliance, Security Incidence and Event Monitoring (SIEM), Disaster Recovery, Capacity Planning and Incident Response Planning.
Our Enterprise Architecture services represent the core of our Managed IT solutions. We focus on strategic solutions that align with your business objectives. Our customized solutions are designed to deliver secure, resilient and scalable networks. We focus on protecting your infrastructure, minimizing costs and keeping the network performing optimally so you can focus on running your business..

SAVE YOU FROM DARKNESS

Pen Testing

Architecture Services

Consultancy

Digital Forensics

Password Auditing

Security Audit

Vulnerability

Awareness Program

Social Engineering
Please call us or submit a question or comment, please fill out the form. We will respond as soon as possible..